Phishing with past email conversations
Phishing attackers are constantly finding new ways to trick us into clicking on links or opening files. Recently, it has become common for them to use past email conversations to appear credible.
A typical example of how this can happen:
- A user receives an apparently legitimate email containing a continuation of an email conversation in which the recipient was previously a party to the conversation. The attacker likely got hold of the conversation from previous leaks from some party involved in it.
- The email contains a request to open a document that is said to be related to the case. The prompt can look different.
- The recipient of the email will access the document by following a link. If the document is opened, malicious code may be executed.
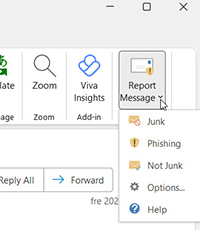
If you receive such an email, you can report it as Phishing via the Report Message menu, which you will find at the top right of the opened email. The email is then deleted and information is sent to Microsoft.
Always pay attention to the sender's address, the language of the message and whether you expect to receive a file sent to you. Don't hesitate to double-check with the person before opening an attachment or clicking on a link if you are unsure - and do so via a different way of contact than by replying to the email.
Read more about how you can protect yourself from phishing External link, opens in new window.
External link, opens in new window.