Centrally managed updates on JU's Mac computers
Starting 2024-04-25, a new system for managing updates and upgrades on JU Macs will be implemented using Intune DDM Software Update External link, opens in new window..
Previously, updates were managed by users themselves through computer notifications about new updates. However, it has been too easy to ignore these notifications, and we have struggled to maintain high security on the devices.
Management via Intune:
Updates for macOS 14 Sonoma and onwards will be centrally managed through Intune. This allows for better control over the update process and ensures security across all of the university's Macs. At the same time, it will give users some control over when updates are installed to minimize disruption.
Notifications and reminders:
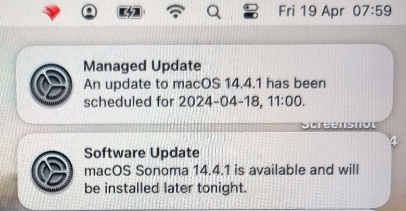
When a new update or upgrade is released by Apple, users will now receive a notification from Intune prompting them to update their computers.
Depending on the importance of the update, users will have a certain timeframe to manually initiate the update.
If the user chooses to delay the update, they will receive repeated notifications with increased frequency.
Automatic installation of updates:
If the update is not initiated by the user within the specified timeframe, the system will eventually automatically start the update process.
What do you as a Mac user, need to do?
- If your Mac already has macOS 14 Sonoma, you don't need to do anything.
- If your computer has macOS version 13 or earlier, you need to manually upgrade to version 14 before the new update management takes effect.
- You can upgrade your computer by opening System Settings -> General -> Software Update.
My computer can't be upgraded to macOS 14, what should I do?
- Ensure that your hard drive isnt full
- Check that the computer is connected to the internet
- Apple stops sending out major macOS upgrades to its older models after about 6-7 years. Discuss the possibility of getting a new computer with your supervisor.
This improvement in security on the university's Mac computers will be followed up with more security-enhancing measures. We will, among other things, explore the possibility of:
- Setting a minimum requirement for which version of macOS is allowed to connect to the school's IT resources (e.g., OneDrive and Outlook).
- Evaluating Microsoft Defender Endpoint for Mac External link, opens in new window.
- Making FileVault External link, opens in new window. mandatory and centrally storing encryption keys in Intune.
